Introduction
The CA Service Desk Manager (SDM) is designed to help IT service desk analysts improve their efficiency. A one-way integration is provided between the system and service desk incidents.
Prerequisites
- User credentials are required to access CA SDM.
- Configure to receive an access token in CA SDM.
CA SDM Configuration
CA SDM uses two-level authentication to access the system REST services. To configure the system, access CA SDM to receive access tokens, token URL, and payload details. Also, a RESTful API call can be viewed to update a CR. Create and update CR payloads are required to add an event to the system.
Get access token
To access a token make a REST access request call:
- Use
http://<ca_sdm_server_url>/caisd-rest/rest_accessto access credentials. - Use basic authentication and retrieve an access key from CA SDM.
For basic authentication, base64-encoded credentials are used in headers: Authorization: BASIC Base64EncodedCredentials.
With SDM, the same header is accepted: Authorization: SDM Base64EncodedCredentials.
Replace Authorization as SDM Base64EncodedCredentials.
Accept : application/jsonA POST call made with these details retrieves the access token.
The access key in the response is used to make the RESTful API calls.
Example response
{
"rest_access": {
"@id": 406101,
"@REL_ATTR": 406101,
"@COMMON_NAME": 796354189,
"link": {
"@href": "http://<ca_sdm_server_url>/caisd-rest/rest_access/406101",
"@rel": "self"
},
"access_key": 796354189,
"expiration_date": 1585800576
}
}RESTful API call to create a CR
URL: <ca_sdm_server_url>/caisd-rest/cr
Example payload
{
"cr": {
"customer": {
"@COMMON_NAME": "System_SD_User"
},
"description": "Created from REST API Java Examples code"
}
}Headers
Access Key from the first call is used in X-AccessKey header as X-AccessKey: $access_key:
Accept : application/json Content-Type : application/json X-Obj-Attrs : chg_ref_num X-AccessKey : 730838761Example response to a POST call
{
"cr": {
"@id": 677195,
"@REL_ATTR": "cr:677195",
"@COMMON_NAME": "REQ-265395",
"link": {
"@href": "http://<ca_sdm_server_url>/caisd-rest/cr/677195",
"@rel": "self"
}
}
}RESTful API call to update the CR
Update the details of a CR details for creating an integration event during configuration:
Endpoint URL: <ca_sdm_server_url>/caisd-rest/cr/677445
Headers
Accept : application/json Content-Type : application/jsonExample payload
{
"description": "Update description"
}Example request
{
"cr": {
"@id": 677445,
"@REL_ATTR": "cr:677445",
"@COMMON_NAME": "REQ-265451",
"link": {
"@href": "<ca_sdm_server_url>/caisd-rest/cr/677445",
"@rel": "self"
}
}
}In both cases, @COMMON_NAME in response is the ticket number used by the CA service desk. Operations on the ticket are performed with reference to @id used in the URL.
OpsRamp Configuration
Install the Integration
- From All Clients, select a client.
- Go to Setup > Account.
- Select the Integrations and Apps tab.
- The Installed Integrations page, where all the installed applications are displayed. Note: If there are no installed applications, it will navigate to the Available Integrations and Apps page.
- Click + ADD on the Installed Integrations page. The Available Integrations and Apps page displays all the available applications along with the newly created application with the version.
- Search for CA Service Desk Manager using the search option available.
Note: Alternatively, you can use the All Categories option to search. - Click ADD on the CA Service Desk Manager tile. The Inbound tab is displayed.
Configure the Integration
Based on your requirements, you can configure Inbound, Outbound or both.
Configure the Inbound (From CA Service Desk to OpsRamp)
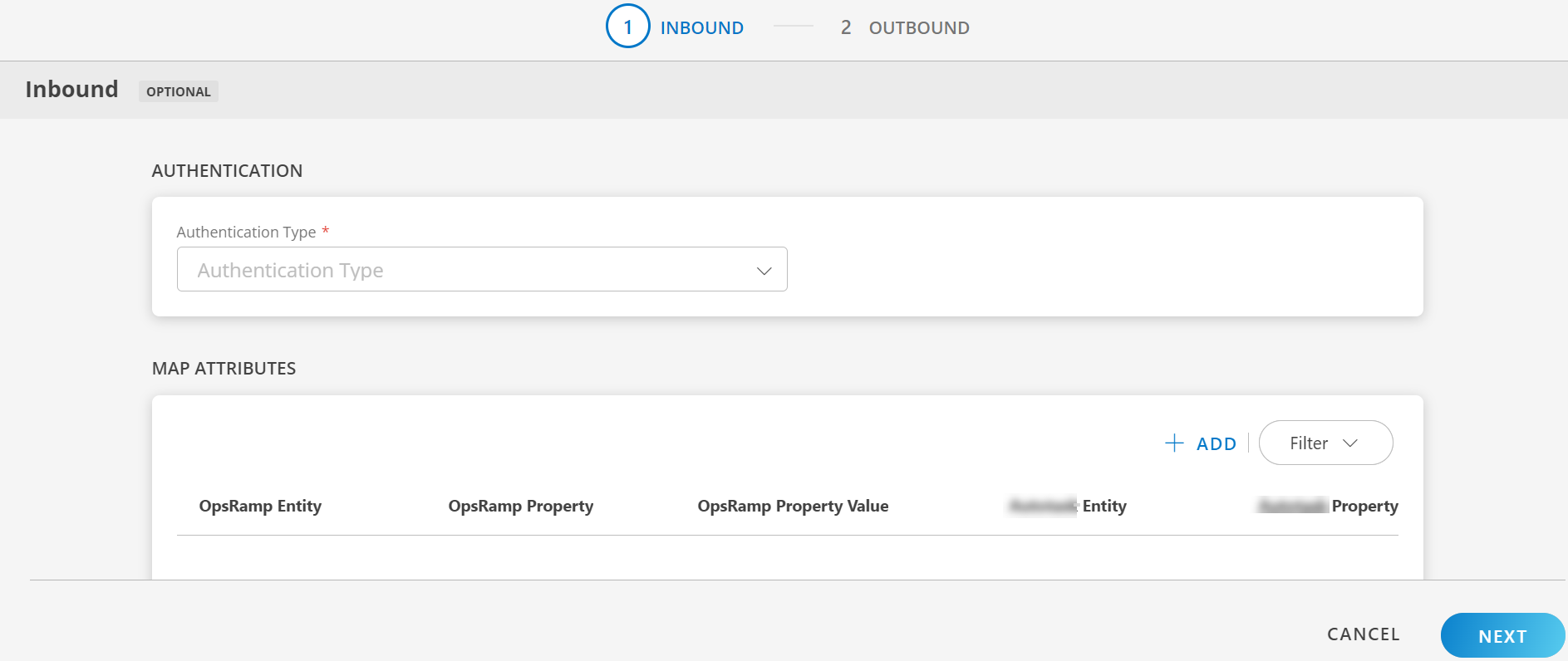
To configure the inbound, follow these steps:
- Authentication: Select OAUTH2 from the Authentication Type dropdown and click on Generate Key to generate the Key and Secret.
Note: Keep a copy of the token as the information will not appear again. Read information about the Access Key. - Map Attributes: Map OpsRamp entity attributes with CA Service Desk Manager attributes.
- Click +Add from the Map Attributes section.
- From the Add Map Attributes window, enter the below information:
- OpsRamp Entity: Select the Opsramp entity from dropdown.
- OpsRamp Property: Select the Opsramp property from dropdown. It will change based on entity selection.
- CA Service Desk Entity: Enter the CA Service Desk entity.
- CA Service Desk Property: Enter the CA Service Desk property.
- Click +Property Value in the Property Values section, and enter CA Service Desk Property Value and OpsRamp Property Value and click Save.
Note:- The Property values section appears based on the OpsRamp Property selected.
- To add property values, click +Property Value.
- To map more attributes, click +Entity.
- Properties:
- Click +Properties from the Properties section.
- Enter the values for the Properties and Value fields and click Save.
Note: To add properties, click +Properties - Click Add Map Attributes.
- Click Next. The Outbound tab is displayed.
Configure the Outbound (From OpsRamp to CA Service Desk)
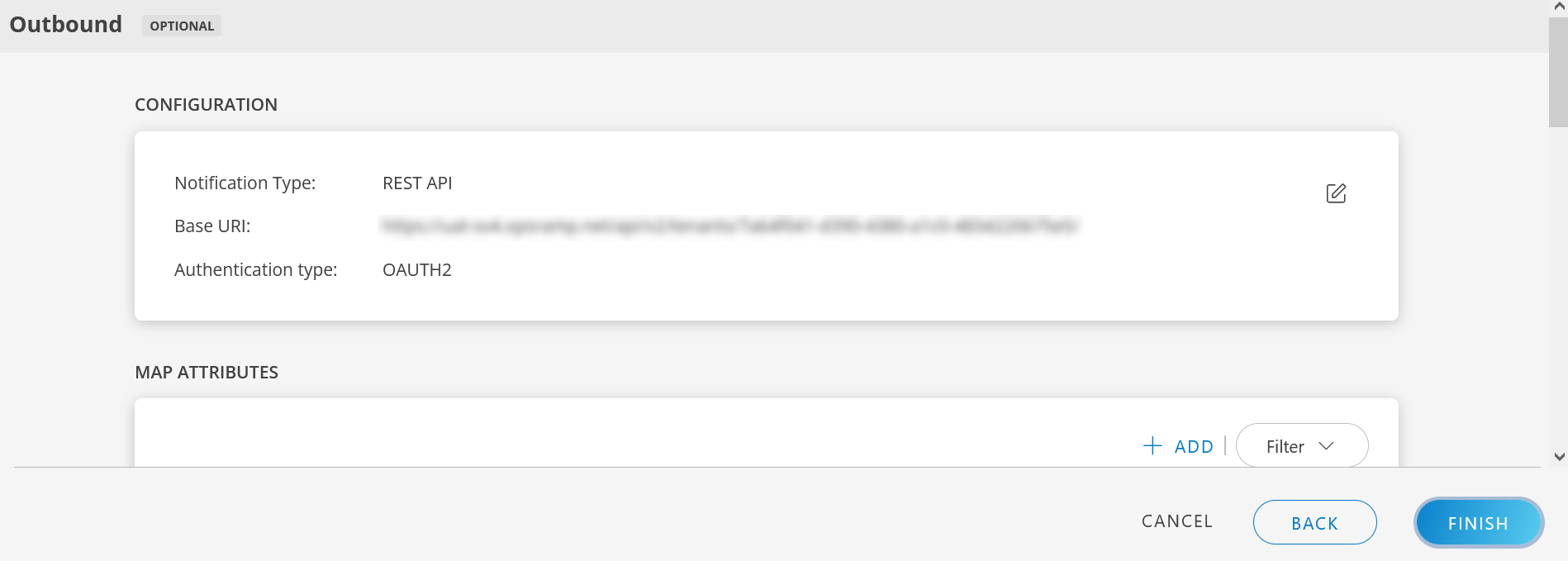
To configure the outbound, follow these steps:
- Configuration: The notification details to trigger integration events are displayed.
- Base URI:
https://{subdomain}.com/arsys/services/ARService?server=oncaservicedesk-s&webService=OpsRamp_CreateIncident - Notification Type: Select the Notification Type. Available options are REST API and SOAP API.
- Authentication Type: Based on the Notification Type selected, the Authentication Type differs. Available options are Basic, OAuth2, JWT, None.
- Base URI:
- Map Attributes: From the Map Attributes window, enter the below information:
- OpsRamp Entity: Select the OpsRamp entity from dropdown.
- OpsRamp Property: Select the OpsRamp property from dropdown. It will change based on entity selection.
- CA Service Desk Entity: Enter the CA Service Desk entity.
- CA Service Desk Property: Enter the CA Service Desk property.
- Click +Property Value in the Property Values section, and enter CA Service Desk Property Value and OpsRamp Property Value and click Save.
Note:- The Property values section appears based on the OpsRamp Property selected.
- To add property values, click on +Property Value.
- To map more attributes, click on +Entity.
- Click Add Map Attributes .
- Events: Events are for sending notifications when an action is performed on OpsRamp entities.
- Click Add in the Events section.
- Enter a name for the event.
- Select the Entity, Entity Type, and Entity Type Event from the drop-down lists.
- (Optional) Under Advanced Settings, enter the values for Property, Operator, and Value and click Save.
- From Actions:
- Select Use Parent Configuration checkbox to inherit parent configuration.
- Enter Endpoint URL.
- Select the Notification Type. Available options are REST API and SOAP API.
- Select the Authentication Type. Based on the Notification Type selected, the Authentication Type differs. Available options are Basic, OAuth2, JWT, None.
- Select the web method.
- Headers:
- Click +Add and enter/select the header name and value.
- Click Save to save the header name.
- (Optional) Click +Add to add more _headers
- Enter the Payload.
- Response:
- Click +Add and enter/select the response name and value.
- Click Save to save the response name.
- (Optional) Click +Add to add more responses.
Note:- The event is created, only if you provide the response properties.
- You cannot enter more than four responses.
- (Optional) Attachment: In the Attachment section, provide inputs in the Process Type, Attachment Endpoint URL, and Web Method fields.
- Attachment Headers: In the Attachment Headers section, provide inputs in the Name and Value fields and click on Save.
- Enter the payload in the Attachment Payload box.
- Enter the Key and Value in the Attachment Response section.
- Click Add Event. The event is added.
There are some actions you can perform on the Events.
See here for more details.
Integration response mapping configuration
Response mapping configuration is mainly based on the response payload that is received in third party payload; below are a few examples for response mapping configuration:
- sample response payload to mapping the id in response mapping:
{ "id":"INC0001", "type":"incident", "tool":"servicedesk" }external ticket id = $id
We need to append $ to the value - sample response payload to mapping the id in response mapping:
{ "result":{ "id":"INC0001", "type":"incident", "tool":"servicedesk" } }external ticket id = $result.id
- Sample response payload to mapping the id in response mapping
{ "result":[ { "ticketDetails":{ "id":"INC0001", "type":"incident", "tool":"servicedesk" }, "Description":{ "display_value":"testing description", "value":"validating" } } ] }external ticket id = $result[0].ticketDetails.id
- sample response payload to mapping the Incident Number in response mapping
{ "result": { "Incident Number": "INC0001", "type": "Incident" } }external ticket id = $result[‘Incident Number’]
- Failures: In the case of failure in integration, an Email is sent to the user about the failure in integration.
To configure failure notification:- Click add from the Failures section.
- Select notification type as Email.
- Enter the email address(es) in the To and CC fields
- Click Add Failure Notifications. The details are added.
- Click Finish. The integration is installed.
Actions on Integration
You can perform actions on an integration.
- See here for more information.
Actions on Event
Follow these steps to perform actions on the events:
- Click on the integration name.
- Navigate to Outbound tab > Events section.
- Hover over the event name.
- Click the actions (three dots) menu. A popup appears with options.
- Copy Id: To copy an event Id.
- Edit: To edit the event details.
- Save as: To save an event name.
- Validate: Validate if the event is successful.
- Select Json or Form.
- Json: Enter the payload and click on Validate.
- Form: Enter the property and value in the fields and click on Validate.
A green tick appears if the event is successful
- Json: Enter the payload and click on Validate.
- Select Json or Form.
- Remove: To remove an event.
Audit Logs
View logs from the Audit Logs tab. You can view if the event was successful or not.